Threats and Concerns in the Open Web
As the Web opened its doors for eCommerce, one motivating security concern was whether and how users could safely provide credit card numbers and related information to sites across the Internet. As users connected to this new resource, they were also concerned about malware infiltrating their computers.
What were the threats and concerns?
Malware: Viruses, Trojan Horses, and Botnets
Malware proliferated, and it became expected practice (at least on Microsoft Windows platforms) that scanning
programs with current signature subscriptions should be installed and running on users' machines
as a defensive measure. Later in the era, it became increasingly common for attackers to infect
users' machines with malware that enabled the attackers to control the infected systems, not only
compromising their sensitive information but also assembling victims into botnets to attack other targets.
Identity Theft
Users became concerned that their financial or other personal information would be stolen from them, enabling
miscreants to impersonate them. Beginning in 2002, U.S. states enact laws requiring detected
security breaches to be disclosed.
Phishing and Social Engineering
Users were misled into accessing impostor sites that appear like legitimate sites but are actually malicious.
Initially, this was most commonly achieved via links sent in email messages. Site names may confuse
users by appearing similar to those of sites they intend to access.
Government Control of Cryptography
In the security community, there were major debates through the 1990s about
use, strength, and export of cryptography, a fundamental building block for distributed security, as
the campaign button suggests.
Participants included Government officials, technology developers, and an emerging cypherpunk movement.
In 2000, US restrictions on export of cryptographic technology were relaxed significantly.
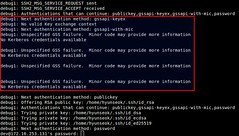
Remote Command Security
The Internet's early Telnet protocol was widely used for
login sessions to remote systems, but transferred passwords and other data without encryption. Increasingly, and
particularly for remote server management,
the newer Secure Shell (SSH) protocol supplanted its use.
 Information Security History: A Virtual Overview
Information Security History: A Virtual Overview