Security Techniques in the Open Web
As the Web and its user community grew, a range of security technologies were developed and implemented in browsers and servers. Much of the focus concerned protection of web traffic from interception or tampering while in transit across the Internet.
What security techniques and developments were important?
Secure Sockets Layer (SSL) and Transport Layer Security (TLS)
Early browser developer Netscape Communications created the cryptographic Secure Sockets Layer (SSL)
protocol, subsequently standardized as Transport
Layer Security (TLS). SSL applied cryptography to help
make the Web safe for customers' credit card transactions. It was soon
adopted and implemented within browsers to authenticate web sites to users, triggering display of the
familiar but
sometimes confusing lock icons.
Public Key Infrastructure (PKI) and certificates
PKI was a hot and
hyped technology in the Internet bubble of the late 1990s, launching companies and high expectations.
In actual practice, sites registered
public-key certificates to authenticate themselves to users, but SSL's capabilities to
authenticate users with their own certificates didn't replace many passwords.
IP-layer security (IPsec)
Many companies used IPsec-protected tunnels
to allow remote employee access
into corporate networks, or to link their distributed sites across the Internet. Most Web-facing business sites
used the higher SSL/TLS protocol layer with its browser-level support to protect their customers' sessions, however.
Firewalls
As Internet-based attacks became more common, firewalls became a standard tool that organizations
applied to restrict traffic into and out of their networks. Host-based firewalls also became common,
filtering communications into and out of individual computers. The fact that many networks became effectively
reachable only via the Web's http and https protocols served as one motivation for layering other functions
on top of them, leading to the creation of web services.
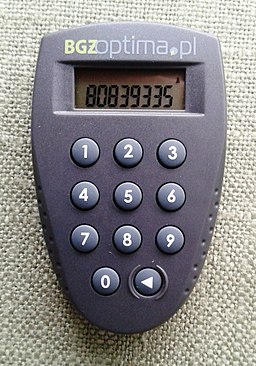
Passwords and authenticator devices
Most users authenticated to most of their sites with passwords, leading either to user inconvenience in
managing them or to user vulnerability by sharing the same password across multiple sites.
Some companies issued two-factor authentication devices to their employees, avoiding many risks
associated with passwords.
Malware scanning
Virus infections became common, and subscriptions to anti-virus packages (providing updated malware signatures
as new malware modules were circulated and detected) became a prerequisite for safe use of
Windows PCs. Research cited in this
2004 article found that it was likely for a new PC, once connected
to the open Internet, to become infected within 20 minutes, likely before protective updates
and anti-malware software would be installed. Early
in the era, most malware could be detected using static signatures, but it became more difficult for these techniques
to keep up as malware became increasingly sophisticated and dynamic.
Federated authentication
Significant effort went into
development of federated authentication technologies
like the Security Assertion
Markup Language (SAML),
which enabled receiving sites (relying parties (RPs)) to accept user authentications performed by others
(identity providers (IdPs)), but early adoption was limited partly because prospective relying parties hesitated to
support and rely on independent identity providers.
 Information Security History: A Virtual Overview
Information Security History: A Virtual Overview